At tecsens we have private cloud environments for business organizations where we can host all information systems and applications.

- Private Cloud Platform based on Proxmox.
- 24x7x365 monitored physical and virtual infrastructure.
- Access to detailed monitoring tools, alerts, and performance metrics.
- Architecture equipped with technologies and functionalities.
- Tolerance to physical host and storage failures.
- Guaranteed availability. In the event of a crash of one of the dedicated servers in the cluster, the system restarts the virtual machines on another physical server.
- Physical hosts distributed across Availability Zones.
- Fault-tolerant storage systems with SATA or SSD disks.
Tecsens Private Cloud Architecture
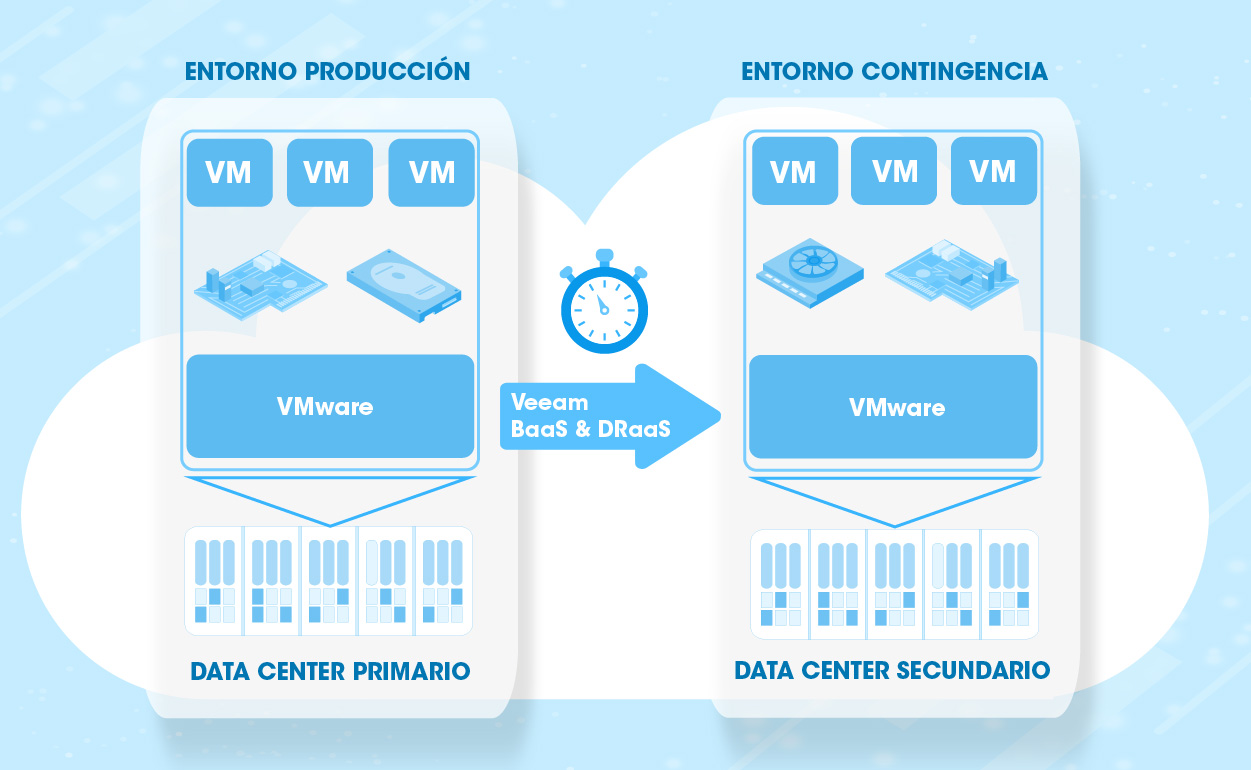
The main difference of the Tecsens Private Cloud environment is that our workloads are delivered protected by Backup and Replicas with customised RTO and RPO for each customer under Veeam technology.
En Tecsens somos partner Cloud & Service Provider oficial de Veeam.

Available licences
SPLA LICENCE:
The Microsoft SPLA (Services Provider License Agreement) is a licensing programme that allows you to rent monthly licences for the provision of cloud solutions.
Types of SPLA licences available:
- Windows Server
- SQL
- RDS
For any other type of licensing, please contact us.
Your company in the hands of specialists
TECSENS SENSE & TECNHOLOGY
Empty
What exactly is a dedicated virtual server?
It is a service where the customer can make use of compute and storage resources exclusively. These being not shared with any other client.
Does my dedicated virtual server include if requested by the firewall service?
All our servers are delivered protected with virtual firewall. This can be shared among different clients or dedicated, so in this case, it would be unique to the customer.
Does my virtual dedicated server include the backup service if I request it?
All of our dedicated virtual servers are protected by a rigorous contingency plan and business continuity. With the prestigious Veeam Backup&Replication software, TECSENS has different levels of protection of our customers’ systems or data. From which you can find everything from file or database backups, to replication of the entire virtual infrastructure in our contingency datacenter. Being able to secure the best RTOs and RPOs to our customers.
How do I access my server?
Using peer-to-peer VPN, access VPN, or by filtering remote access exclusively for your location from which you’ll access your server.
For what purposes can I use a dedicated virtual server?
A dedicated server can be used for multiple purposes, for example, web services, databases, file sharing systems, business intelligence calculation systems, remote desktops can be installed… Etc.
Can I virtualize my server using a hypervisor?
The vast majority of servers allow them to be virtualized and therefore it is possible to upload the workloads you run to the private cloud.
What operating systems can I deploy to a dedicated virtual server?
We can install the vast majority of GNU/Linux, Windows Server or OSX distributions.
What security measures are in place to protect my data?
TECSENS applies rigorous security measures to ensure data availability, integrity and confidentiality. From the physical infrastructure part of datacenter to the data themselves. Measures include access control systems, data encryption systems, data backup, and replication.
Find out more…
Interview about our merger between TECSENS and Signia
TECSENS and Signia: a strategic merger to offer comprehensive technological solutions. The magazine Relación Cliente has recently published an interview in which we analyse the details of the merger between TECSENS and Signia. This union marks a key milestone...

CloudTel PBX makes your day-to-day life easier
At Tecsens, we know that every minute counts in your work routine. That's why we want to introduce you to the solution, CloudTel PBX, the virtual PBX that not only optimizes business communications, but also offers you practical tools to simplify your day-to-day life....
Need to talk to an expert?
Our offices
- Paseo de la Castellana 171, 4º Izq, 28046 (Madrid)
- C/Figueres 8 Despacho 12, 08022 (Barcelona)
- Edisonstraße 63 House A, 1st Floor, 12459 (Berlin)
![]() Monday to Thursday 9.00-18.30h Friday 9.00-15.00h
Monday to Thursday 9.00-18.30h Friday 9.00-15.00h





